Autoclicker.exe ⚡ Tested
: Functionality for taking screenshots (YARA detection).
: 2e67d5e7d96aec62a9dda4c0259167a44908af863c2b3af2a019723205abba9e . Platform : Windows Executable (PE32/PE32+).
: Third-party download sites or unofficial repositories are notorious for bundling "Autoclicker.exe" with adware, trojans, or backdoors . Technical Specifications (Sample Data) File Size : Typically ranges from 844 KiB to 12.46 MB . Autoclicker.exe
: If you did not intentionally download a specific auto-clicking tool from a verified source, treat "Autoclicker.exe" as a high-threat file. You can verify your specific file by uploading it to Jotti's Malware Scan or VirusTotal for a multi-engine check. AutoClicker.exe - Hybrid Analysis
The analysis of "Autoclicker.exe" (as of April 2026) shows varied results depending on the specific file version and source. While many legitimate auto-clicking tools use this generic filename, several versions have been flagged for or highly suspicious behavior by automated analysis platforms . Security Analysis Summary : Functionality for taking screenshots (YARA detection)
: Programs like OP Auto Clicker are generally considered safe when downloaded from their official site, though they may still trigger "suspicious" alerts due to their core function of controlling mouse input.
: Some scanners flag legitimate auto-clickers because they use AutoIt, a scripting language often associated with malware, or because the software mimics mouse behavior that resembles trojan activity. Common Trusted vs. Risky Sources : Third-party download sites or unofficial repositories are
: Reports from ANY.RUN and Hybrid Analysis have assigned threat scores as high as 75/100 , tagging some samples as malicious or evasive. Detected Malicious Behaviors : Data Theft : Attempting to steal personal data.
 System Overload 2026Fri Feb 27
System Overload 2026Fri Feb 27 Decadence Arizona 2025 | The Portal of I11usionsTue Dec 30
Decadence Arizona 2025 | The Portal of I11usionsTue Dec 30 John Summit | Bird's Nest 2026Sat Feb 07
John Summit | Bird's Nest 2026Sat Feb 07 LevitySat Feb 14
LevitySat Feb 14 Odd Mob | Phoenix Warehouse Project 2 Year AnniversaryFri Mar 13
Odd Mob | Phoenix Warehouse Project 2 Year AnniversaryFri Mar 13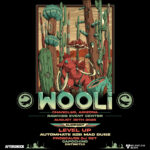 WooliSat Aug 30
WooliSat Aug 30 SHAQ's Bass All-Stars PhoenixSat Aug 16
SHAQ's Bass All-Stars PhoenixSat Aug 16 GrabbitzFri Nov 07
GrabbitzFri Nov 07 Obsidian 2025Fri Nov 07
Obsidian 2025Fri Nov 07 Chris LorenzoSun Aug 31
Chris LorenzoSun Aug 31 RB Writer Picks: Top Tracks of 2025Courtney Longhurst
RB Writer Picks: Top Tracks of 2025Courtney Longhurst Enter The Portal of Beats: A Guide to The Music of Decadence AZMarcus Arrieta
Enter The Portal of Beats: A Guide to The Music of Decadence AZMarcus Arrieta RB Exclusive Interview: Braydon Terzo Headlines DarkstarKaden Kleinschmidt
RB Exclusive Interview: Braydon Terzo Headlines DarkstarKaden Kleinschmidt The EDM Subgenres of 2025 Making Marks On PlaylistsAmra Alic
The EDM Subgenres of 2025 Making Marks On PlaylistsAmra Alic Knock2 Scheduled to Launch Decadence Night One Into the StratosphereChase Courtney
Knock2 Scheduled to Launch Decadence Night One Into the StratosphereChase Courtney Capozzitech house
Capozzitech house ISOxo
ISOxo Bella ReneeElectronic pop
Bella ReneeElectronic pop YetepDance
YetepDance